Some issues are easier to to figure out how to file than others, so I've compiled some of common ones I've filed to improve bicycling infrastructure in NYC.
When a pedestrian signal is broken or missing, you can file a Pedestrian Signal Complaint or Request.
If a large dumpster blocks a bike lane, you can "Report a large amount of trash" under the "Roadway" section on the Trash or Debris in Street page. Unfortunately, this does happen:

When overgrown plants narrow greenway bike paths, DOT staff have told me to "Report trash or debris on a traffic island or median with landscaping," which can be under the "Traffic Island or Median" section of the Trash or Debris in Street page. "Bike path/greenways" is one of the options in the "Additional Details" field. You can't currently pick a street segment to report a stretch of a greenway where plants are overgrown, but you can provide this information in "Additional Location Details."
When a catch basin cover has the unsafe kind of grate that can catch a bicycle wheel instead of a completely flat grate, you can report it as "Sunken, damaged, or raise" on the Catch Basin Complaint page. Here's an example of an unsafe catch basin cover in a bike lane:

I use the following template for the issue description when reporting unsafe catch basin covers:
The catch basin at the {NW, NE, SE, SW} corner of the intersection of STREET and STREET has an unsafe grate for bicyclists. The current catch basin cover has the type of holes that can catch a bicycle wheel and cause a bicyclist to crash. The City needs to replace this unsafe catch basin grate with one of the flat grates with shorter holes that are safe for cycling. STREET is a major bike route in BOROUGH and leaving this unsafe grate in place endangers many bicyclists.
When there's a pothole in the bike lane, you can report it to NYC DOT by filling out their pothole form.
When a street's surface has been patched up poorly or is otherwise uneven, you can file a Street Resurfacing Request.
If there's a street improvement you'd like to see, anything from a new stop sign or traffic signal to adding bulb outs at an intersection to requesting a new protected bike route, you can contact NYC DOT via their general webform. Sometimes, these requests get closed in error with an autoresponder that isn't really all that topically relevant to the issue, and it's worth refiling them a second time noting that the automatic reply didn't address your issue alongside the original reference number. You might want to refile under a slightly different relevant category - many requests can be made under multiple categories, and if you and your neighbors want to all write in about something, it can be especailly helpful to have different types of relevant requests for the same issue. Also, reporting unsafe conditions for bicyclists doesn't just help get them fixed - these reports can also be used in court cases to show the City has created negligent conditions for bicyclists.
As always, you can elevate any concern you file on 311 or through DOT's forms by contacting your local Community Board and Council Member with the reference number.
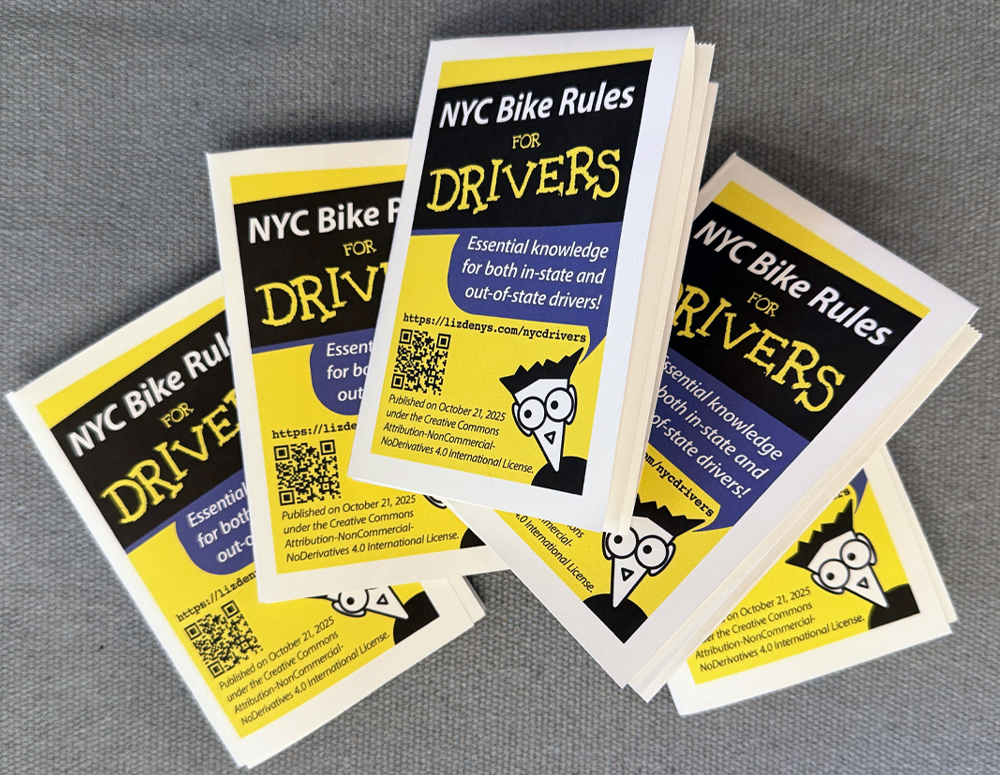
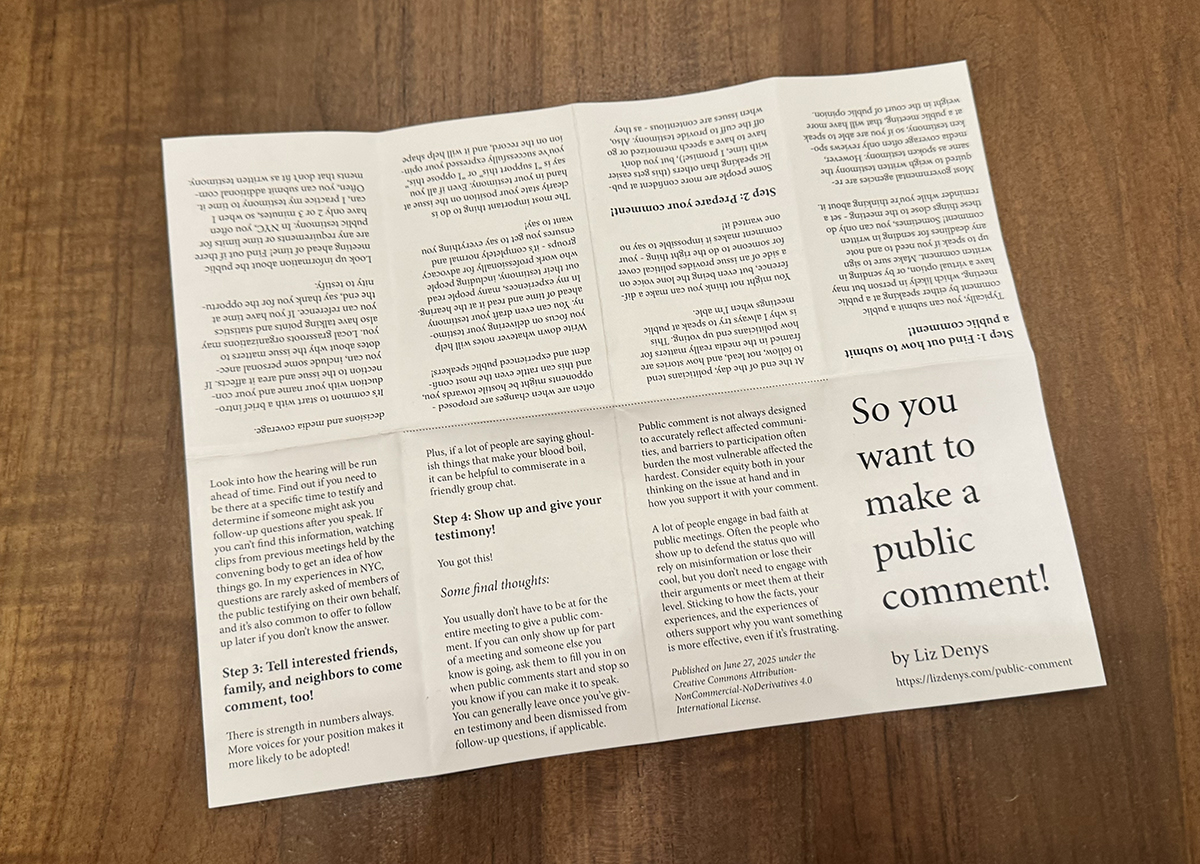
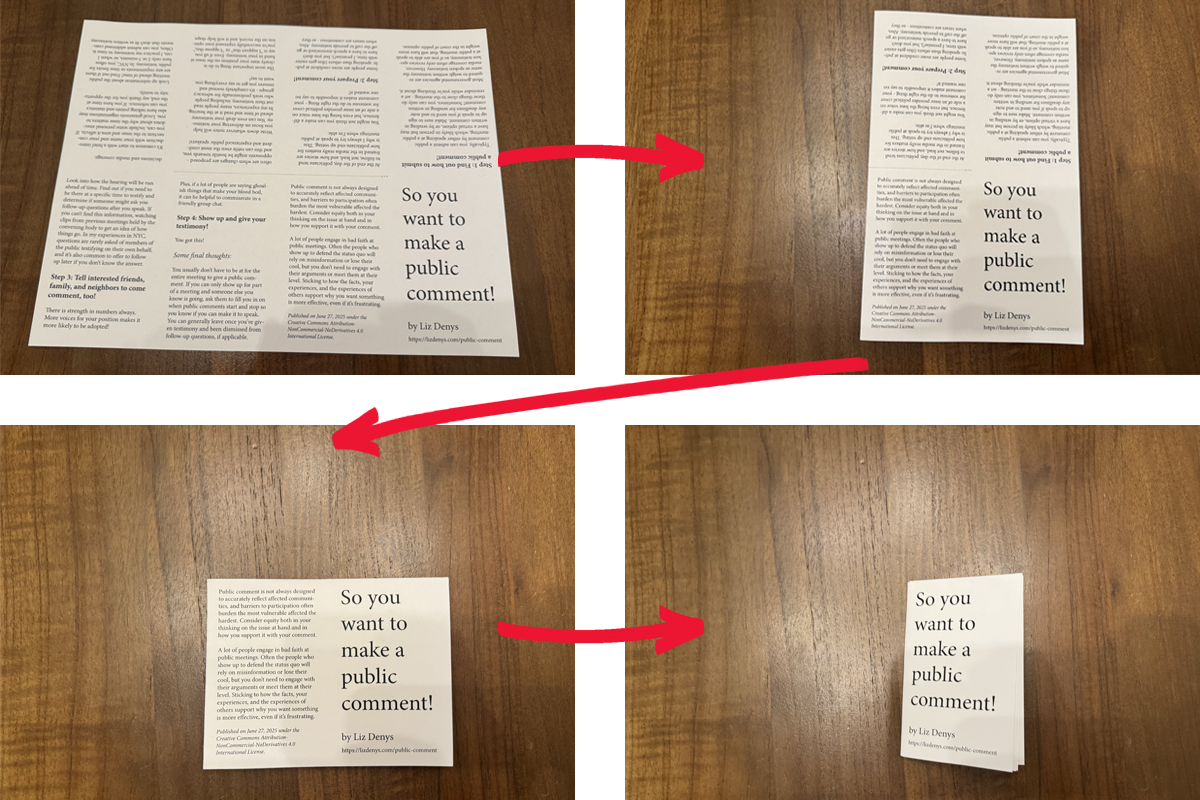 When you open the piece of paper, each of the pages should fit fully within a set of folds.
When you open the piece of paper, each of the pages should fit fully within a set of folds.
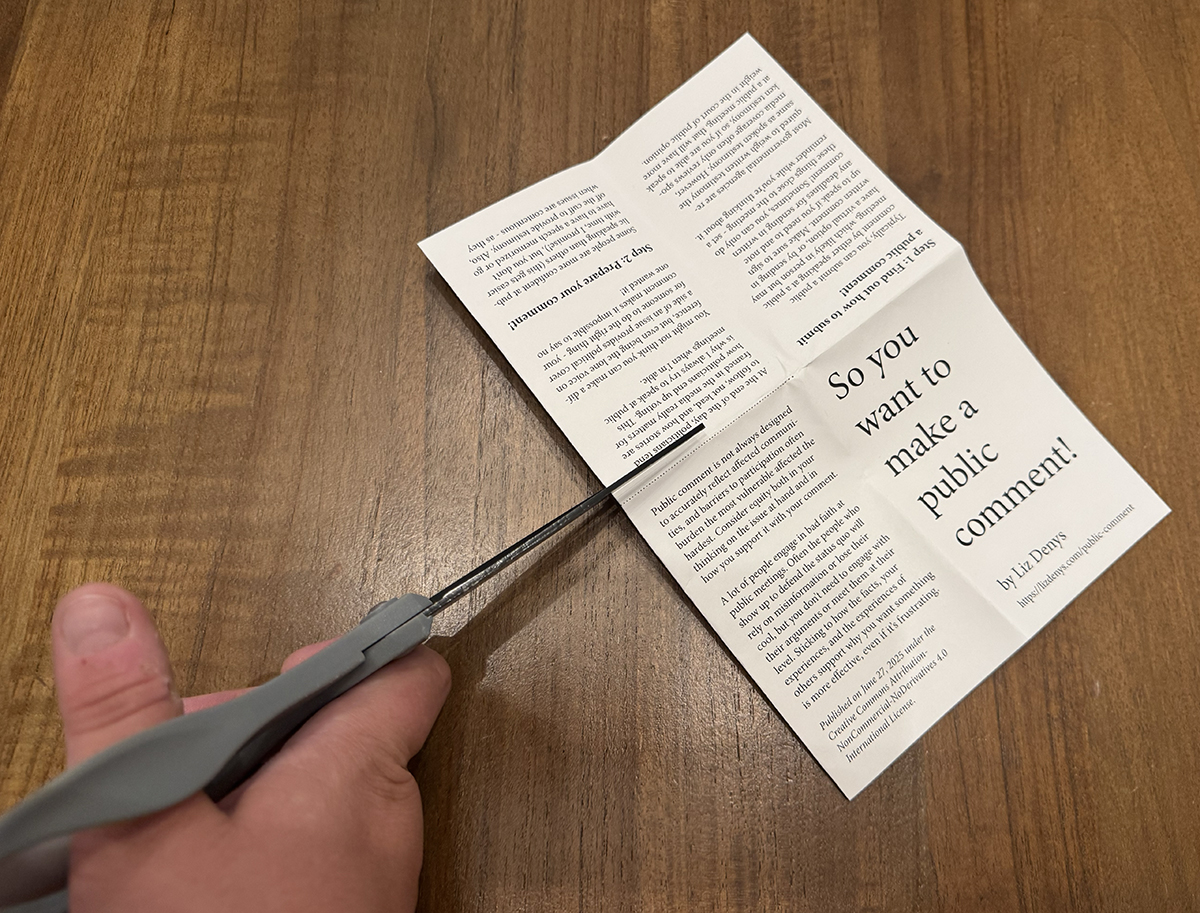 When you reopen your paper, there will be a slit in the middle of the sheet.
When you reopen your paper, there will be a slit in the middle of the sheet.
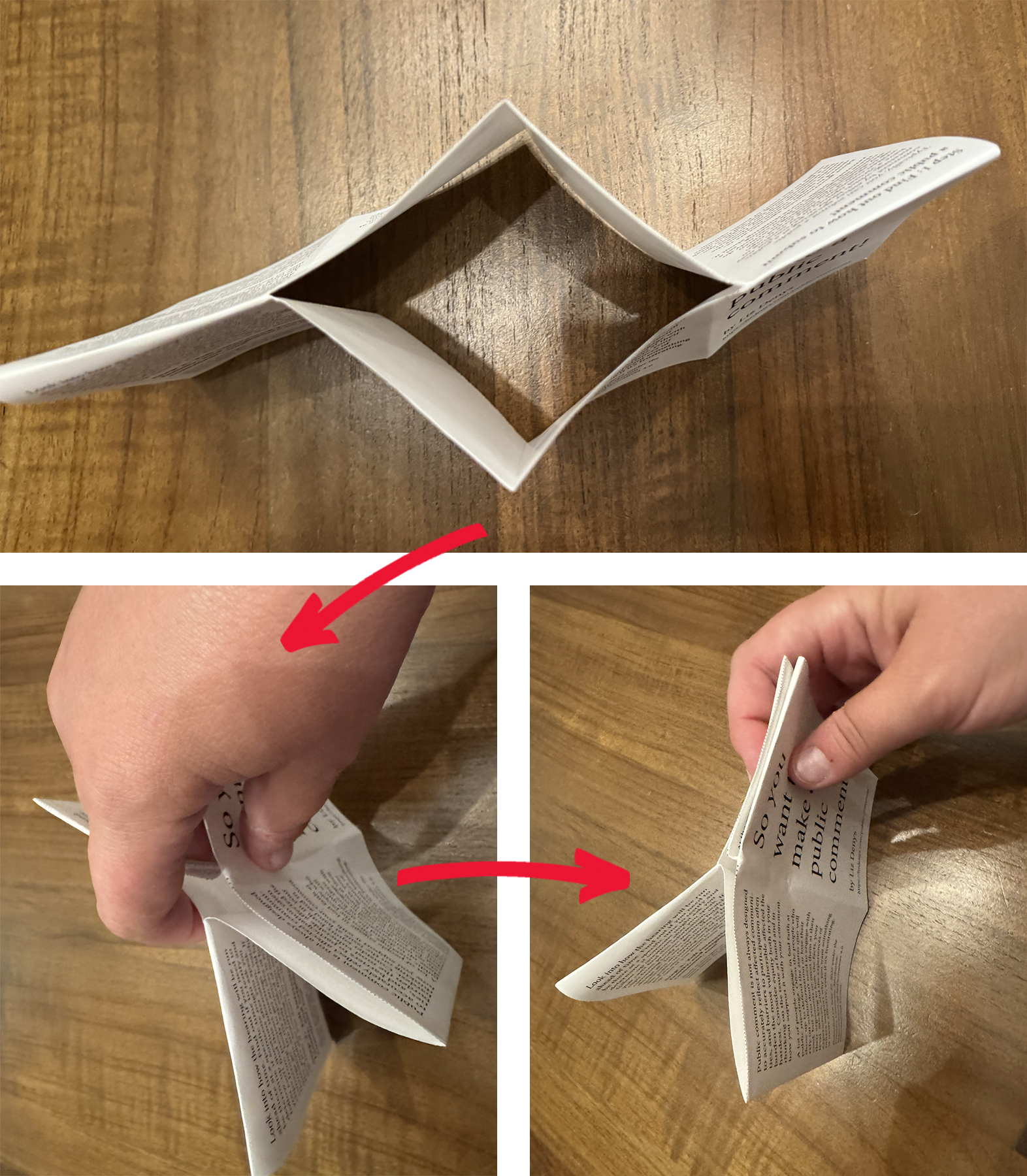 Make sure the cover is on the front!
Make sure the cover is on the front!